Cybersecurity Daily — Mar 09, 2026

Photo: blogger.googleusercontent.com
Monday, March 9, 2026
The Big Picture
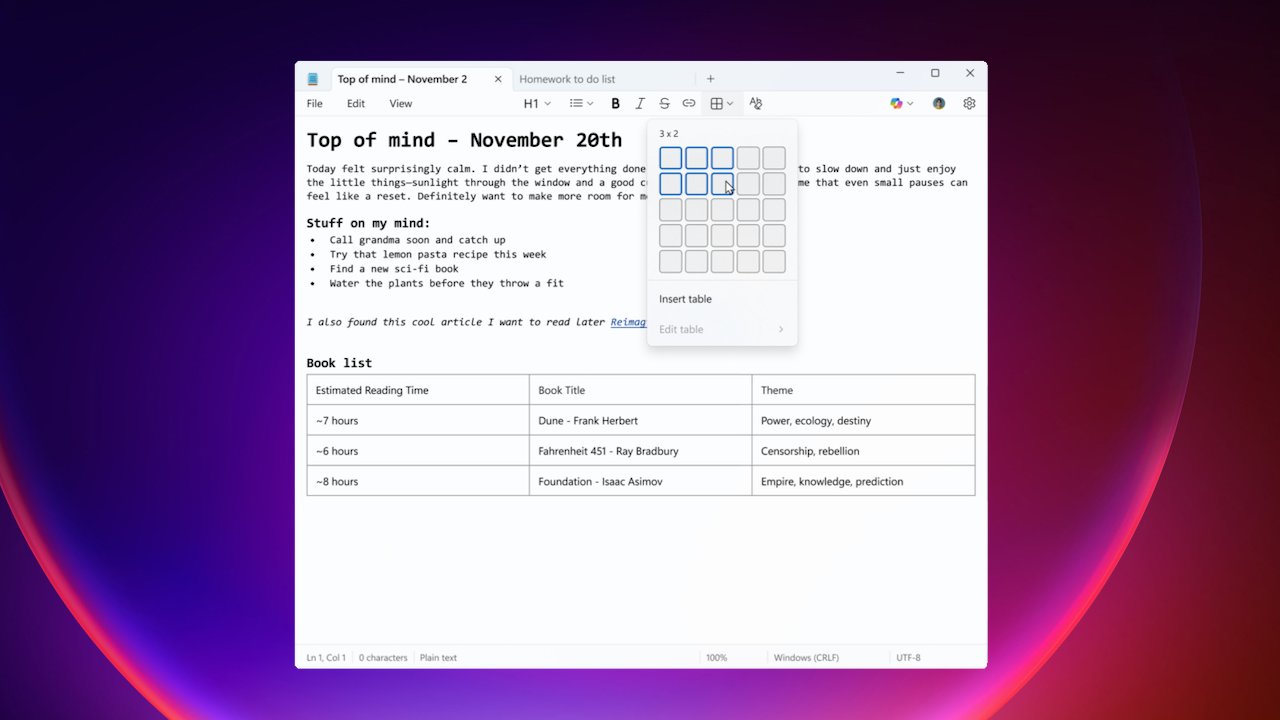
Attackers aren't breaking down walls this week — they're walking through doors you already opened. A Chrome extension you installed years ago just got sold to someone who turned it into a credential harvester, and a Notepad file that looks like meeting notes can now execute code on your machine. The theme is weaponized trust: the most dangerous things in your environment are the ones you stopped thinking about.
Today's Stories
Your Chrome Extension Just Changed Hands — And Now It's Stealing Your Passwords
There's a quiet marketplace where developers sell their browser extensions — users included — to the highest bidder. That market just produced one of the cleanest supply-chain attacks of the year.
Two Chrome extensions, QuickLens and ShotBird, turned malicious after an ownership transfer in early February. The new owners pushed a poisoned update on February 17 that expanded permissions, embedded command-and-control functionality, and quietly dismantled your browser's built-in security headers — Content-Security-Policy, X-Frame-Options — on every page you visited. In plain terms: the extension removed your browser's seatbelts while you were driving.
What came next was worse. The malicious version injected fake Chrome update prompts, delivered a file called googleupdate.exe disguised as a Google-signed installer, and deployed a second-stage payload that dumped credentials, scraped Gmail inboxes, raided Facebook Business Manager accounts, and exfiltrated payment data from web forms. Researchers traced the chain from a Reddit user noticing weird console.log messages on every site they visited — a small thread-pull that unraveled the whole operation.
As of March 9, 2026, Google removed QuickLens from the Chrome Web Store and disabled it in affected browsers. ShotBird remained accessible as of March 9, 2026. If you have either extension installed, remove it now. Then do the thing nobody wants to do: open your extension list and audit everything you haven't thought about in six months. That's the single most valuable action you can take today.
For IT teams managing browser fleets: treat ownership transfers and sudden update timestamps on widely-deployed extensions as suspicious events. Consider enforcing enterprise-only extension policies and blocking auto-updates until you can validate publishers.
That Notepad Patch From Last Month? PoC Exploits Are Now Public
Source: inbuzzer.com
The February Patch Tuesday story nobody finished reading just got significantly more urgent. Public proof-of-concept exploit code for CVE-2026-20841 — an 8.8-rated remote code execution flaw in Windows Notepad — is now circulating on GitHub, and the Zero Day Initiative just published a detailed technical breakdown.
The attack is almost insultingly simple. An attacker sends you a crafted Markdown file (the lightweight formatting used in README files and developer docs). You open it in Notepad. You click what looks like a normal hyperlink. Notepad launches an unverified protocol that loads and executes a remote file with your permissions. Game over.
The real danger is psychological. Markdown files have never been considered risky. A file labeled Project_Notes.md wouldn't raise eyebrows — especially opened in an application people have trusted since childhood. That implicit trust is the entire attack model.
Here's the kicker nobody mentions: this patch requires manual action. Store apps don't always auto-update. You need Notepad version 11.2510 or later — go to the Microsoft Store, search Notepad, and hit Update. Don't assume it installed itself. For enterprise teams: push the patched version via Intune or managed Store channels, add EDR rules for Notepad spawning network calls, and consider blocking .md attachments at the mail gateway until you've confirmed coverage. The MSRC advisory has the canonical details.
Salt Typhoon Compromises Telecom Giants Worldwide — Call Records, Texts, and Audio Stolen

Source: techcrunch.com
New reporting attributes a sprawling set of telecom intrusions to Salt Typhoon, a China-linked espionage cluster that has compromised carriers and service providers across dozens of countries. The victim count is in the hundreds of organizations, with stolen data including call records, text messages, and audio — some tied to senior government officials.
The entry point: compromised Cisco routers and other edge network gear. This is infrastructure-level espionage — not stealing passwords, but tapping the pipes that carry everyone's communications. If you operate carrier or peering infrastructure, treat routing and edge device integrity as the primary threat surface. Inventory and patch edge routers, rotate credentials used for lawful-intercept or retention systems, and treat unusual routing changes as high-priority alerts.
For everyone else, the takeaway is sobering: your phone calls and texts may traverse infrastructure that's already been compromised. End-to-end encrypted messaging isn't paranoia — it's hygiene.
Good-Faith Bug Reporter Gets Threatened With Criminal Charges
This is the most-discussed cybersecurity story on Hacker News right now (917 points), and it matters because it's about the system that's supposed to prevent breaches.
Yannick Dixken, a platform engineer, discovered that his sports insurance company's portal used sequential user IDs combined with default passwords — meaning anyone could guess their way into other people's accounts, including accounts belonging to minors. He reported it responsibly through Malta's CSIRT. Two days later, he didn't hear from the IT department. He heard from the company's lawyers, who suggested his actions could constitute a criminal offense.
The vulnerability was an IDOR (insecure direct object reference) — a beginner-level flaw. The response was a chilling-effect masterclass. Organizations that answer disclosure with lawyers instead of engineers are telling the world something important: they care more about reputation than about the data they're supposed to protect. Amid legal threats to researchers, voluntary bug reporting can decline, and those bugs can sit unfixed until someone less ethical finds them.
If your organization runs a vulnerability disclosure program, this is a case study in exactly what not to do.
Cloned AI Tool Sites Deliver Malware in "InstallFix" Campaign
A new malvertising campaign dubbed InstallFix is cloning download pages for popular AI tools and developer utilities, then swapping the install commands with malicious ones. Victims reach convincing look-alike sites through search ads, where a single copy-paste or curl command fetches an infostealer instead of the expected binary.
This is the same trust-exploitation pattern as the Chrome extension story, elevated to search ads and installer flows. For developers and data scientists: treat any install instructions reached via ads or unofficial mirrors as suspect. Consider locking high-value engineers behind allow-listed download repositories or internal artifact mirrors. Verify checksums. Always.
⚡ What Most People Missed
Anthropic's AI found 22 Firefox vulnerabilities in 2025 — 14 high-severity. Working with Mozilla, Anthropic's Claude model discovered nearly a fifth of all high-severity Firefox bugs patched in 2025. Amid this, AI-assisted vulnerability discovery appears to be maturing; defenders who aren't experimenting with it may fall behind attackers who do.
A critical Nginx UI bug (CVE-2026-27944, CVSS 9.8) lets unauthenticated attackers download and decrypt full server backups. Flagged by Thailand's national SOC, this affects a popular web-based admin frontend — not Nginx core — that often ends up exposed to the internet. If you've got Nginx UI on a public IP, lock it behind VPN or SSO today.
ImageMagick's CVE-2026-30937 is scored "medium" but the real-world risk is higher. The heap buffer overflow is classified as "local," but in containerized web apps, image processing is fully attacker-controlled via uploads. Your profile-photo feature could be a crash-or-RCE vector. Update to ImageMagick 7.1.2-16+ or 6.9.13-41+ and rebuild containers.
CISA is flagging active exploitation of Apple iOS and macOS flaws. Multiple vulnerabilities linked to a mobile exploit kit are on the KEV catalog as of March 2026. If you manage Apple fleets, push MDM updates immediately — mobile device compromise is a direct path to corporate account takeover.
Ontario's health-sector ransomware disclosure lagged the actual incident by a year. The newly confirmed ransomware attack hit a home-care vendor in spring 2025 but was only publicly labeled ransomware this month. If you track "2026 incidents," you're missing compromise windows that started much earlier — align vendor risk reviews with when attackers got in, not when headlines land.
📅 What to Watch
- If Google announces policy changes around Chrome extension ownership transfers, it means the ShotBird/QuickLens research and community pressure finally moved the needle on a gap that's been exploited since at least December 2025's DarkSpectre wave.
- If CVE-2026-20841 PoC code appears in phishing kits on criminal forums, expect a wave of
.mdfile email attacks within days — the gap between "researcher demo" and "commodity phishing vector" is closing fast. - If major cloud providers issue advisories about React Server Components RCE (a critical pre-auth vulnerability trending in CVE feeds today), it means providers may need to revoke shared runtime privileges, rotate credentials, and enforce emergency mitigations in server-side renderers — forcing operations teams into high-priority change windows.
- If the researcher behind the Dixken disclosure names the company or files a legal counterclaim, this moves from community grievance to active legal precedent — worth watching for anyone who runs a bug bounty program.
- If BeyondTrust CVE-2026-1731 exploitation expands beyond current confirmed incidents, it could signal ransomware affiliates pivoting toward privileged access management infrastructure — an especially damaging entry point for enterprise environments.
Patch Notepad. Audit your extensions. Forward this to someone who still thinks .md files are harmless.
See you tomorrow. — CS Daily