The Lyceum: Cyber Intelligence Daily — Apr 18, 2026

Saturday, April 18, 2026
The Big Picture
This week's theme is institutional memory — and the lack of it. CISA just confirmed attackers are actively exploiting a 17-year-old Microsoft Office bug, Germany finally put real names to the people who ran REvil and GandCrab, and CERT-UA is publishing APT28 advisories faster than Western press can translate them. The through-line: the oldest unpatched bugs and the oldest unnamed criminals both catch up eventually.
Attackers aren't chasing novel zero-days; amid widespread use of automated scanners that find unpatched systems, a 2009 Excel flaw on an unpatched workstation pays off today as well as it did 17 years ago.
What Just Dropped
- CVE-2009-0238 — Microsoft Office Excel: actively exploited, added to CISA KEV April 14, federal patch deadline April 28. A 17-year-old remote code execution bug now confirmed in active use.
- CVE-2026-32201 — Microsoft SharePoint Server: actively exploited, added to CISA KEV April 14, federal deadline April 28. Improper input validation enabling server compromise.
- CVE-2023-36424 — Microsoft Windows: actively exploited, added to CISA KEV April 13, federal deadline April 27. Out-of-bounds read flaw — low-profile but now weaponized.
- CVE-2020-9715 — Adobe Acrobat: actively exploited, added to CISA KEV April 13, federal deadline April 27.
- CVE-2026-34197 — Apache ActiveMQ: patched, CVSS 8.8, actively exploited (KEV). A 13-year-old RCE in the message broker; audit exposed instances now.
- Nexcorium (Mirai variant): new DDoS botnet targeting TBK-branded DVRs via default credentials; active recruitment underway.
- CVE-2025-24813 PoC — Apache Tomcat RCE: fully automated exploit script dropped on GitHub within the last 24 hours. Patch or expect opportunistic scanning by Monday.
Today's Stories
A 17-Year-Old Microsoft Office Bug Is Back From the Dead — And CISA Says It's Being Used Right Now
● United States
If your organization hasn't patched Microsoft Office since the Obama administration, someone may already be inside your network.
Over two batches on April 13 and April 14, CISA added nine vulnerabilities to its Known Exploited Vulnerabilities catalog — the government's official "patch these or explain why" list, which only accepts entries with evidence of real-world exploitation. The headline entry is CVE-2009-0238, a Microsoft Office Excel remote code execution flaw that is older than the iPad. Alongside it: CVE-2012-1854 (Visual Basic for Applications), CVE-2020-9715 (Adobe Acrobat), CVE-2023-21529 (Exchange Server), CVE-2023-36424 (Windows), CVE-2025-60710 (Windows), CVE-2026-21643 (Fortinet FortiClient EMS), CVE-2026-34621 (Adobe Acrobat), and CVE-2026-32201 (SharePoint Server). Federal agencies have until April 27–30 to patch.
What changes if defenders take this seriously: the assumption that old bugs are dead bugs dies with it. Automated scanners routinely find unpatched systems, and a 2009 Excel flaw on an unpatched workstation pays off exactly as well today as it did 17 years ago. What failure looks like: CVE-2023-36424, a low-profile Windows out-of-bounds read, is the canary. It's the kind of bug that gets skipped in patch cycles because it doesn't make headlines. Watch whether follow-up KEV batches start pulling in more Windows bugs from the 2022–2023 era — if they do, it would indicate attackers have quietly retooled around an entire generation of "not critical enough to patch" flaws.
APT28 Has a New CERT-UA Advisory — And Western Press Hasn't Caught Up Yet
● Ukraine · NATO Europe
Ukraine's national cybersecurity agency published a bulletin this week that hasn't made it into Western reporting — and if your organization runs Microsoft Office, it matters directly.
CERT-UA Advisory #19542 documents the Russian state-sponsored group APT28 (also tracked as UAC-0001) continuing to exploit CVE-2026-21509, a Microsoft Office security feature bypass (CVSS 7.8). According to Zscaler's ThreatLabz and SecurityWeek reporting, APT28 weaponized the flaw on January 29, 2026 — days after Microsoft's emergency patch — using phishing emails with geopolitically-charged lures (weapons smuggling narratives, military training documents, meteorological bulletins) that trigger code execution the moment the document opens. No macros. No user interaction beyond opening the file.
The infection chain is the interesting part. Per Trellix, the campaign deploys a multi-stage chain: an initial loader, an Outlook VBA backdoor called NotDoor, and a modified Covenant implant. Command-and-control runs through filen.io, a legitimate cloud storage service — meaning exfiltration looks identical to a user syncing files. That's the whole point. What changes if this spreads: traffic-based detection becomes nearly useless for this campaign, because there's no malicious domain to block. What failure looks like for defenders: Office patches from January still sitting unapplied on executive laptops. The observable signal to watch — whether CERT-UA issues follow-up advisories with new lure themes tied to current NATO or Ukrainian military events. APT28 adapts its pretexts within days of news cycles.
Germany Just Named the Men Behind REvil and GandCrab
● Germany · Russia
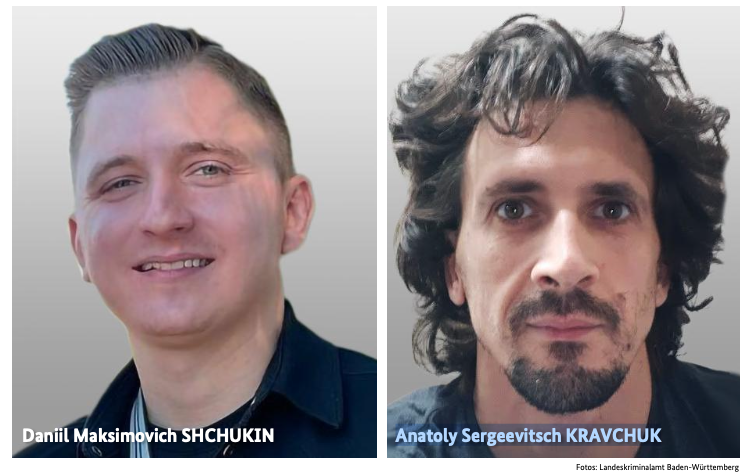
For years, the public face of REvil — one of the most destructive ransomware operations ever — was a forum handle: "UNKN." This week, Germany's Federal Police (BKA) put a name to it.
Per Brian Krebs and BleepingComputer, the BKA identified two Russian nationals as the leaders of GandCrab and REvil between 2019 and July 2021: Daniil Maksimovich Shchukin, 31, who posted under UNKN/UNKNOWN, and Anatoly Sergeevitsch Kravchuk, 43. German authorities attribute at least 130 extortion cases against German companies to the pair, with at least 25 victims paying $2.2 million in ransom and total damages exceeding $40 million. Globally, REvil and GandCrab extracted hundreds of millions — REvil's 2021 Kaseya attack alone briefly took down hundreds of managed service providers in a single afternoon.
This is a doxing operation, not an arrest. Both men are believed to be in Russia, where extradition is a fiction. What changes: anonymity as operational security gets stripped away. Affiliates think twice before joining a crew whose leaders are named and sanctioned; travel outside Russia becomes difficult; family and financial networks become visible to Western investigators. What failure looks like: Shchukin and Kravchuk simply resurface under new handles with the same affiliate base, and the naming becomes a trophy rather than a deterrent. The signal to watch — retaliatory ransomware activity against German critical infrastructure in the next two weeks. Reports of incidents at German hospitals or utilities in that window would be consistent with a retaliatory response.
A Fortra GoAnywhere Flaw Is Being Exploited Again — And This Time It's a 10.0
If your organization runs Fortra GoAnywhere MFT — a managed file transfer platform popular in healthcare, finance, and government — move this to the top of the queue.
CVE-2025-10035 is a deserialization flaw (attackers send a crafted package that tricks the software into executing their code) in GoAnywhere MFT. It carries a CVSS score of 10.0, the maximum. Per CISA's KEV catalog, it's confirmed ransomware-linked and actively exploited. Per Microsoft's April 6 threat intelligence blog, the ransomware actor Storm-1175 was exploiting this flaw a full week before public disclosure — deploying it in high-tempo Medusa ransomware operations against web-facing assets.
The pre-disclosure exploitation window is the part that should alarm people. If Storm-1175 had working exploit code before the CVE was public, they may have obtained it from a broker, discovered it independently, or had access to unpatched information from the vendor's own disclosure pipeline. Any of those three is bad. What changes if this pattern continues: "patch fast" stops being sufficient defense for internet-facing appliances, because the race starts before the starting gun. What failure looks like: organizations that assumed routine quarterly patch cycles covered them now face double-extortion ransomware — GoAnywhere handles exactly the kind of sensitive data (payroll, patient records, financial filings) that makes data-theft extortion catastrophic. The observable signal — watch for Fortra to release updated indicators of compromise, and review transfer logs going back at least 30 days. If you see anomalous activity before the CVE was public, you're not alone.
⚡ What Most People Missed
A "RedSun" proof-of-concept targeting Microsoft Defender surfaced on r/hacking this week, claiming to grant SYSTEM-level privileges on Windows machines. This is Tier 3 signal — one Reddit thread, 410 upvotes, no vendor confirmation and no assigned CVE. But Defender runs with elevated privileges by design, which makes any working local privilege escalation in it the kind of flaw ransomware crews integrate into pre-deployment stages within days. Treat as a watch item; if Microsoft issues an out-of-band advisory in the next 48 hours, that's confirmation.
A Cisco AsyncOS zero-day has reportedly been under active attack since late November 2025 — roughly four and a half months of silent exploitation against the operating system underpinning Cisco's Secure Email Gateway and Secure Email and Web Manager. Cisco's December advisory warned customers to check for compromise but had no patch available. An email security gateway that's been compromised for months isn't an entry point — it's a collection platform, watching every credential, internal message, and attachment that transited it.
NIST's April 17 cutback on CVE data enrichment is creating a real operational gap. Vulnerability management teams that relied on NVD for enriched severity context and CPE mapping are now seeing delayed or incomplete entries. Industry coalitions are forming to fill the gap, but in the interim, triage is harder and exploit windows are wider.
Sophos has documented ransomware crews running QEMU-based virtual machines inside compromised Windows hosts — hiding their tooling in a guest OS the endpoint agent can't see. Campaigns tracked as STAC4713 and STAC3725 use the VM as a staging environment for credential theft and reconnaissance. Hunt for unauthorized QEMU binaries, SYSTEM-level scheduled tasks invoking virtualization tools, and virtual disk files masquerading as DLLs. [Source: SecurityLab.ru — Russian]
Operation PowerOFF was customer-mapping, not just infrastructure takedown. Police in 21 countries seized 53 domains, arrested four, and — per SecurityLab — gained access to data tied to more than three million user accounts of DDoS-for-hire services. The 75,000 warning notices sent to buyers is the real story: casual "rent a booter" threat models now carry legal consequences. [Source: SecurityLab.ru — Russian]
From the Foreign Press
CERT-UA #21075: Attackers Are Impersonating CERT-UA Itself to Deliver AGEWHEEZE
Between March 26–28, the threat cluster UAC-0255 sent phishing emails using cloned CERT-UA branding, linking to a lookalike domain (cert-ua[.]tech) whose HTML was copied wholesale from the real cert.gov.ua. Victims who clicked downloaded a password-protected archive containing AGEWHEEZE, a Go-based remote access trojan. The campaign targeted government, healthcare, education, finance, and software development sectors — and per CERT-UA's assessment, it was largely unsuccessful, catching only a few educational staff. But the technique is the warning: even the defender brands organizations are trained to trust are now being weaponized as phishing lures. Source: CERT-UA Advisory #21075 — Ukrainian. No English-language coverage confirmed at time of publication.
CERT-UA: UAC-0247 Intensifying Attacks on Ukrainian Hospitals, Local Government, and FPV Drone Operators
CERT-UA published a detailed technical advisory on the UAC-0247 cluster, documenting a March–April spike in phishing disguised as humanitarian aid notifications. The infection chain uses malicious LNK files, mshta.exe for code execution, scheduled tasks injecting into RuntimeBroker.exe, and a multi-stage loader deploying RAVENSHELL (reverse shell), AGINGFLY (C# backdoor with keylogging and screenshots), CHROMELEVATOR (browser credential theft), ZAPIXDESK (WhatsApp data harvesting), and tunneling tools LIGOLO-NG and CHISEL. The targeting includes hospitals and emergency services, local councils, and — notably — operators of FPV drone software distributed via Signal. Any organization with Ukrainian partners or humanitarian-sector overlap should treat CERT-UA's IoCs as priority hunt data. Source: CERT-UA — Ukrainian. No English-language coverage confirmed at time of publication.
📅 What to Watch
- If Microsoft issues an out-of-band Defender advisory in the next 48 hours, the "RedSun" PoC is real and commodity loaders will have it integrated by the following week.
- If CISA follows its April 13–14 KEV batch with more Windows CVEs from 2022–2023, it would indicate attackers have retooled around an entire generation of "not critical enough to patch" flaws — and your backlog just became a frontlog.
- If German hospitals or utilities report ransomware incidents in the next two weeks, those incidents would be consistent with a retaliatory response to the BKA doxing, and would force German investigators and operators to weigh disclosure benefits against operational risk.
- If Fortra publishes updated GoAnywhere indicators of compromise dated before September 2025, the Storm-1175 pre-disclosure exploitation window was wider than currently believed, and the "patch fast" doctrine needs rewriting for internet-facing appliances.
- If APT28 lure themes shift to reflect new NATO or Ukrainian military events within 72 hours of those events, defenders should expect a much tighter campaign cadence that will blunt signature-based detections and increase the need for behavior-based email analytics and immediate hunt activity.
- If Nexcorium jumps from TBK DVRs to Hikvision or Dahua devices, expect DDoS volume against gaming and e-commerce targets to spike within days — the IoT botnet bench is deeper than the current variant suggests.
The Closer
A 17-year-old Excel file waiting patiently on an unpatched machine, a Russian ransomware boss who spent seven years hiding behind the letters U-N-K-N, and a Cisco email gateway that's been reading everyone's mail since Thanksgiving.
Patch accordingly.
Forward this to the person on your team who still thinks 2009 bugs are "legacy."